 A new strain of ransomware has infected computers, over the past few months. The infection is thought to be spread through infected sports websites, or through a compromised MineCraft installer. Based on experts’ opinions, they state that this strain has a large global “installed” base, which means there are one heck of a lot of computers out there all over the world, with this virus installed…
A new strain of ransomware has infected computers, over the past few months. The infection is thought to be spread through infected sports websites, or through a compromised MineCraft installer. Based on experts’ opinions, they state that this strain has a large global “installed” base, which means there are one heck of a lot of computers out there all over the world, with this virus installed…
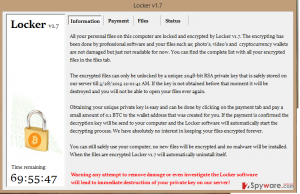
It’s called “Locker”, and sat silently in infected computers, until midnight May 25, 2015.
At that time, it woke from its slumber and reared its ugly head, and wreaked havok in an ugly way.
Bleepingcomputer has a support topic that is 14 pages long, and they received 100s of emails from consultants all over the world. Similar websites with topics related to this new strain are suddenly posted on all the major support boards, AV forums, etc.
Here’s what “Locker” does:
- A series of Windows services are used to install Locker on the computer, and encrypt data files.
- During the install process, Locker will check if the computer is a virtual machine, and will terminate installation if detected.
- Encrypts data files with RSA encryption, and does not change the file extension.
- After the encryption, it deletes your c:/shadow volume copies, and displays its ransom interface.
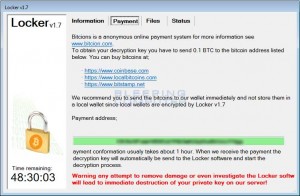
- If you backups failed and you are forced to pay the ransom, once the payment is confirmed, the ransomware will download the private key, and automatically decrypt your files.
 The files that are encrypted have the following suffix extension: .doc, .docx, .xlsx, .ppt, .wmdb, .ai, .jpg, .psd, .nef, .odf, .raw, .pem, .rtf, .raf, .dbf, .header, .wmdb, .odb, .dbf. Locker does not change the file extension, so users will simply receive error messages from their applications that the file is corrupted.
The files that are encrypted have the following suffix extension: .doc, .docx, .xlsx, .ppt, .wmdb, .ai, .jpg, .psd, .nef, .odf, .raw, .pem, .rtf, .raf, .dbf, .header, .wmdb, .odb, .dbf. Locker does not change the file extension, so users will simply receive error messages from their applications that the file is corrupted.
Once the files are encrypted, a Bitcoin ransom is demanded from victims. Once payment is confirmed, victims are provided with a “private key” in order to retrieve their data.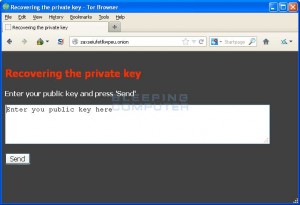
By Time of Publication:
CyberCriminal has remorse? Or he’s made so much money already, he’s pulling out of this campaign, or he’s gotten cold feet & is afraid of getting caught by law enforement, or damaged by a local cyber mafia. Either way, he claims the release was “a mistake”, and has uploaded a CSV file with a dump of the encryption keys. He states that automatic decryption of all infected computers will start on June 2nd.
CyberCriminal states, “I am the author of the Locker ransomware and I’m very sorry about that has happened. It was never my intention to release this. I uploaded the database to mega.co.nz containing “bitcoin address, public key, private key” as CSV. This is a dump of the complete database and most of the keys weren’t even used. All distribution of new keys has been stopped.”
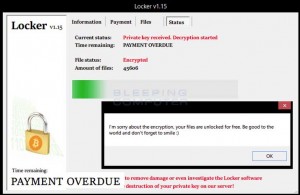 This seems very fishy. If you build code like this, you know exactly what you are doing (and the fact that it was a ‘sleeper’ shows months-long careful planning). If he was really remorseful, he’d refund everyone’s money (which hasn’t happened). So far, it’s not clear if current infection vectors (infected websites/ads etc) have been turned off yet.
This seems very fishy. If you build code like this, you know exactly what you are doing (and the fact that it was a ‘sleeper’ shows months-long careful planning). If he was really remorseful, he’d refund everyone’s money (which hasn’t happened). So far, it’s not clear if current infection vectors (infected websites/ads etc) have been turned off yet.
We can assume that this CyberCriminal wanna-be, is exactly that. He’s a talented coder that sees all these other ransomware viruses/malware being very lucrative, and wants some of that money action. However, he’s not yet experienced, because a “mix-up” like this would not happen with a professional CyberCrime gang.
If you have infected computers, there is a chance you can find the decryption key in this database:
https://mega.co.nz/#!W85whbSb!kAb-5VS1Gf20zYziUOgMOaYWDsI87o4QHJBqJiOW6Z4
This file does not seem to be malicious, based on a brief virustotal analysis. It does contain a large quantity of RSA keys and Bitcoin addresses. OPEN AT YOUR OWN RISK, until further analyses are completed.
TbyD will keep you posted, as more information is released.
Got Cyber-Bugs?
Call 1-204-800-3166
For Cyber-Extermination!
Leave a Reply