ALERT: New Ransomware Targets MS Office 365 Users
A new strain of the Cerber Ransomware is targeting MS Office 365 email users with a massive attack that has the ability to bypass the Office 365’s built-in security tools.
A report recently released by cloud security provider Avanan shows a massive zero-day attack targeting Office 365 users with phishing emails containing attachments with malicious files.
Microsoft reported in its 1st quarter of 2016 that there are almost 18.2 million Office 365 subscribers. And while Avanan does not specify the number of users that have been hit by the ransomware, Avanan does state:
“While difficult to precisely measure how many users got infected, roughtly 57 pecent of organizations using Office 365 received at least one copy of the malware into one of their corporate mailboxes during the time of attack.”
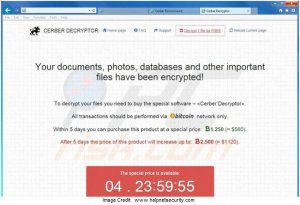
The Cerber Ransomware uses the ever-popular social engineering to try to trick users to allow macros, very similar to the recent Locky and Dridex attacks. The difference is that Cerber not only encrypts user files, and displays a ransom note, but it also takes over the user’s audio system to read out its ransom note informing them that their files were encrypted.
How To Protect Yourself
I’d love to tell you that there was some magic potion to sprinkle, or some magic software to download, that would keep you safe from Cerber Ransomware. However, the steps to avoid becoming a victim to this strain of ransomware, are much like the steps to avoid the rest:
- Backups. Backups. Backups. Maintain current, and reliable backups of all pertinent files. Nothing beats a good, reliable backup! Backing up your data now can prevent a lot of expensive headaches in the future.
- AntiMalware Software. Regularly run AntiMalware software to block known strains of ransomware.
- Update. Update. Update. Keep all hardware, software, and Operating Systems up-to-date.
- Educate. Educate. Educate. Make sure employees and coworkers know about current viruses/malware, and what to look for. Print & post our “Red Flag Emails” for easy reference on what to look for in scam emails.
- Install Ad Blockers When Possible. uBlock Origin is a great ad blocker for Chrome and other browsers.
- Block Extensions via Email. A good spam blocker will usually handle this for you.
- Limit permissions. Allow “Read/Write Access Only” when necessary.
- Avoid mapping network shares. If you have to use them, hide them whenever possible. This is sometimes as simple as appending a “$” to your share name.

Leave a Reply