ALERT: Voice Mail CyberScam
CyberCriminals have found a new way to trick people into infecting their PC with ransomware.
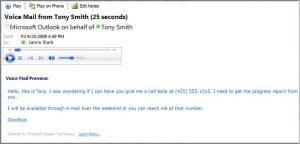
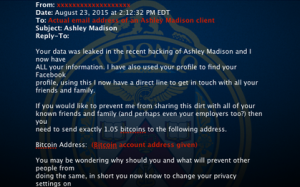
This time, it looks like a Microsoft email that tells you about a voice mail that was left for you, and asks you to click to play the voice mail.
The email looks similar to the one below:
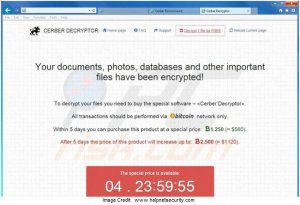
The email has a .zip attachment that supposedly has the voice mail message in a .wav file. However, if you unzip the file, the ransomware will encrypt all the files on your computer, and possibly all files on the network if you have access. The only way to get your files back….is to pay approximately $500 US.
Do not click on links in “voice mail” emails from someone you do not know, and do not open any attachments!