ALERT:
How to Help Prevent Cyber-Infection
Think you’re immune?
So did thousands of banks and other organizations!
Last week, IBM Security report an active CyberHeist campaign using a variant of the Dyre Trojan that has successfully stolen more than $1 million each time, from targeted enterprise organizations.
Since it emerged in June 2014, Dyre has grown even more sophisticated and easy-to-use, spreading the malware through a mall mailing of victims’ contact lists, and targeting organizations instead of individuals, enabling CyberCriminals to go for the bigger payday.
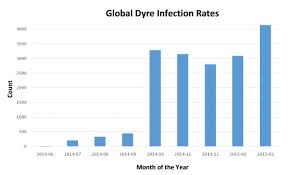
The IBM Trusteer team reported in October 2014, an increase of the infection rate of the Dyre malware from 500 to a startling 3,500 in just 5 months.
The Dyre campaign targets organizations
that frequently conduct wire transfers with large sums of money.
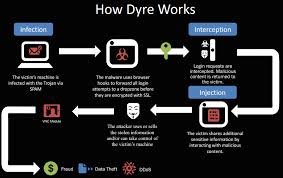
The campaign includes a successful spear-phishing campaign which results in an infection (via Upatra malware). Once the infected PC tries to log into one of the hundreds of bank websites that they Dyre Trojan monitors, a new screen appears (instead of the corporate banking site). The new page explains the website is experiencing issues, and requests the victim to call the number provided to get help logging in. This all results in successfully duping their victims into providing their organizations’ banking credentials. As soon as the victim hangs up the phone, the wire transfer is complete.
The targeted organizations sometimes also experience a Distributed Denial-of-Service (DDos) attack.
Unfortunately for us, Social Engineering still works extremely well for CyberCriminals.
How to Help Prevent Cyber-Infection:
- Train Your Employees. Your organization is only as strong as the weakest link. And your employees have the most exposure, and are usually the most targeted, of your organization. Train them on security best-practices and how to report suspicious activity.
- Have I.T. Conduct Periodic Mock-Phishing Exercises. Have your I.T. department send employees mock-phishing emails, where employees receive emails or attachments that simulate malicious behaviour. Metrics can be captured on how many potential incidents would have happened had the exercise been a real attack. Use these findings as a way to discuss the growing security threats with employees.
- Offer Security Training. Security Training is essential to help employees understand threats, and measures they can take to prevent infections and protect the organization.
- Provide Regular Reminders. Regular reminders for employees about phishing and spam campaigns, and to remind them not to open suspicious attachments or links from both work and personal emails.
- Train Employees in Charge of Corporate Banking. Train them to never provide banking credentials to anyone. The banks will never ask for this information.
Got Cyber-Bugs?
Call 1-204-800-3166
For Cyber-Extermination

Leave a Reply