 Old Ransomware Strain Spreading Through Cloud
Old Ransomware Strain Spreading Through Cloud
An obscure 2-year old ransomware strain is rearing its ugly head, with a REALLY ugly twist
Normally, ransomware is spread through email phishing attacks, exploit kits, removable drives (USB sticks, etc.), or external network shares. However, Virlock is a weird version of ransomware that not only encrypts files, but converts them into a file infector (similar to a virus). It not only infects the usual documents and image-related files, but infects binary files as well.
If that wasn’t enough, Virlock also effectively weaponizes every data file it encrypts, converting each one into a propagation vehicle for the malware itself. This means that the encrypted data files don’t just sit there, but they are used to spread the malware joy to other users through file sharing schemes. It can even be spread via cloud storage and collaboration apps.
How does this work? Like this:
User A and User B are collaborating through the cloud storage app Box, using a folder called “Important”. Both users have some of the files within the folder synced to their own machine.
User A falls for a social engineering attack, and get infected with Virlock ransomware on their own machine, encrypting all their files. It also, at the same time, turns the files into new Virlock infector files, including the files which are synced on Box. So, Virlock also spreads to the cloud folder and infects the files stored there which, in turn, get synced to User B’s machine.
Now, User B clicks on any of the files in the shared folder on their box, the infected Virlock file is executed, and the rest of the files on the machine of User B become infected. The infected files on User B’s machine now become Virlock infectors just like a virus.
The bonus: The scenario isn’t just limited to User A and User B, but will extend to all the users of an enterprise who are collaborating with each other. Clever AND efficient.
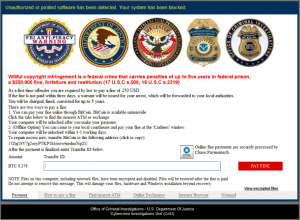
Like other ransomware strains, Virlock asks the victim for a Bitcoin payment in order to release their machine. However, Virlock claims to be an “anti-piracy warning” from the FBI. The message received by the victim states that pirated software has been found on their computer and threatens them with prison and/or a $250,000 file if they don’t pay a $250 “first-time offender” fine. The message may look similar to the one below:
Unfortunately this social engineering method is tried-and-true, and has proven to be a money-maker for the CyberCriminals in past years in an effort to spook victims into paying their “fines” quickly.
The REALLY bad part of this ransomware? It has a high possibility of reinfection. Usually organizations pay Bitcoin ransoms trusting that they’re going to get their files back & not be reinfected with the same ransomware. However, the strength of this ransomware strain is also its weak point. Miss one infected file on some share that most admins forgot about…and sorry, you’re reinfected.
Leave a Reply